We probably had mixed feelings this week when news broke, and social media images emerged, of a teenage burglar caught and restrained in the midst of his attempted robbery, in the early hours of Wednesday morning. Notably, he was overpowered, handcuffed, and then questioned while being filmed. The remarkable restraint shown by the homeowner and former police officer are nothing short of admirable, and revealed some details of the would-be thief, including his name and address. Responses which unsurprisingly were found to be false, perhaps proving that liars are also thieves.
While we may question the motives of the young burglar, and his life choices, it was a sober reminder of the damaging actions by others, perhaps motivated by desperation, greed, or other difficult circumstances. Reportedly, even the RSLPF have noted an ‘unusual spike’ in robberies around the island, meaning that we may also face some degree of risk. In any case, the obvious reminder is for us to be on our guard.
Arguably, physical security breaches as evidenced by broken doors and windows, are relatively easy to detect. What about less obvious break ins? Those working in the ICT arena, specifically those concerned with cybersecurity, have this ongoing concern. While those who use paper files and records may worry about physical security and items stolen from their premises, cybersecurity experts deal with the fear of unseen hackers making off, not with a handful of stolen files from a cabinet, but with the entire loss of digital copies of their data.
With an unusual spike in robberies being experienced —perhaps coinciding with the Christmas season — what steps can we all take? For starters, keeping your wits about you, like a former police officer. At an individual level, staying safe would involve a combination of actions, including the use of security systems, features and devices. Motion controlled lights and camera systems may also appeal to some.
It helps to remember that what makes our ICT gadgets attractive, are not necessarily valuable to a thief. The priceless photos stored on your phone or computer are what truly represents the value of that device, so be sure to make regular backups. Finally, remember that ICT items usually contain security codes and serial numbers. These should be safely stored for ease of reference in case of loss. As always, be safe!
To share your views, contact the author at: www.datashore.net or via The Voice.
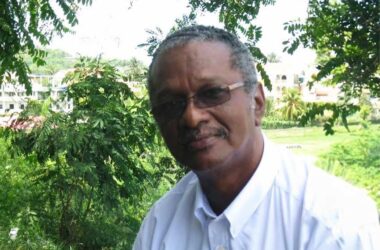
About the Author
Dr. Lyndell St. Ville is an ICT Consultant with a background in environmental and resource science. His expertise includes systems analysis, planning, and capacity building.